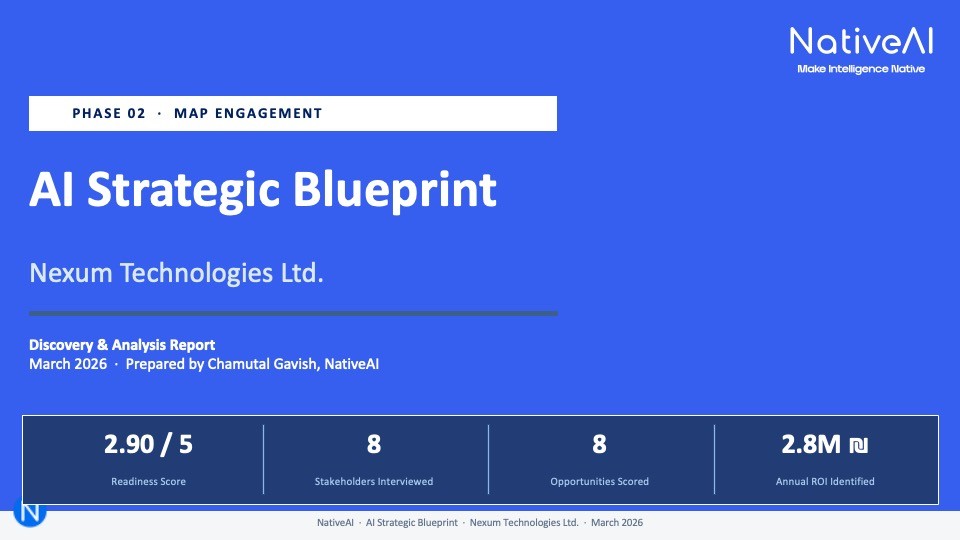
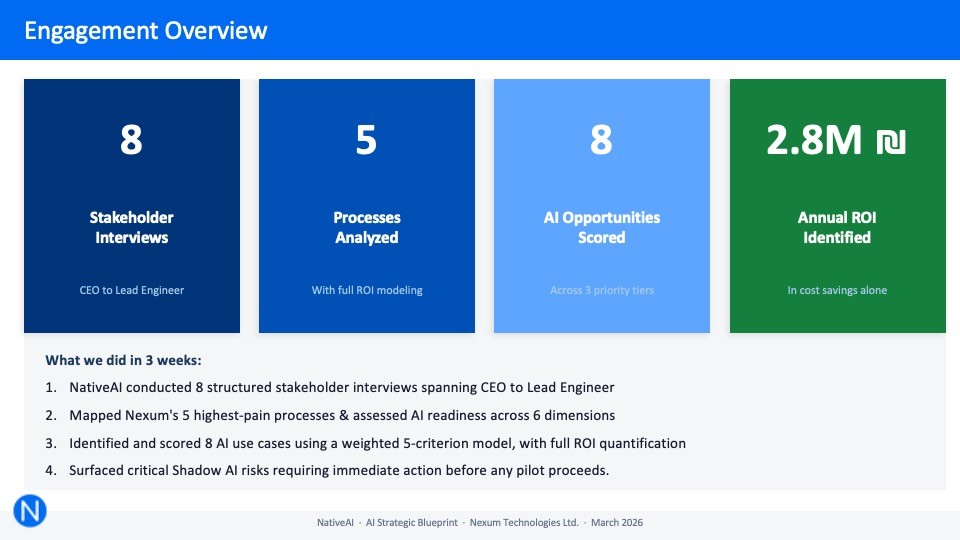
PHASE 02 - map
strategic blueprint
we map all AI opportunities, and build a blueprint based on ROI, effort & complexity
70% of AI initiatives fail because organizations jump straight to tools without understanding their processes. The Blueprint ensures you invest in the right things, in the right order, with clear success metrics from day one.
Timeline
20 days, including opportunities mapping, prioritization and recommendations.
Participants
Executive sponsor, delivery/R&D stakeholders, AI lead, IT.
What We Do
North Star Definition
Together, we define the 2–3 measurable business objectives this AI transformation must achieve. Examples: “Reduce delivery delays by 20%”, “Automate 80% of reporting”, “Cut risk blind spots by half".
Opportunity Mapping
We analyze your delivery workflows: planning, execution, risk management, resource allocation, reporting, and cross-team coordination, to identify where AI can create the biggest leverage.
Ranking and Prioritization
Every opportunity is scored and categorized, according to the value gained and effort invested: quick wins you can capture in weeks, medium-term improvements, and strategic transformations.
Technology Stack Evaluation
We assess which AI tools fit your existing tech environment, security requirements, and team capabilities. No vendor lock-in, we recommend what works for you.
Risk & Governance Assessment
Data privacy constraints, security policies, compliance requirements, and organizational change risks, all mapped before we start.
What You Get
1
AI Strategic Blueprint, a comprehensive 12-month vision and action document
2
AI use cases mapped to your workflows with expected value and investment
3
Recommended technology stack with integration architecture
4
KPI framework - how to measure success for each improvement
5
Risk & governance framework with data privacy and security guidelines
6
Prioritized implementation roadmap: what to do first, second, and third